I didn’t want to write longer title so let me explain what I meant with it. Instead of “unsafe”, I should probably use “relatively not as safe as smaller and not so popular Bittorrent trackers”.
But let me start from the beginning.
Some time ago I read this article in TorrentFreak about using Bittorrent as a DDoS tool. Of course then I tested it on my own server to see how it works. Because I didn’t send too many fake announcements my box didn’t “go down” but I sure got a lot of incoming traffic. That PDF that can be found in the previously mentioned article states that their box received Bittorrent handshake requests long after they sent the last announcement. They suggest that those connections are made by some anti piracy organisations to sniff what kind of torrents you have loaded in your Bittorrent client.
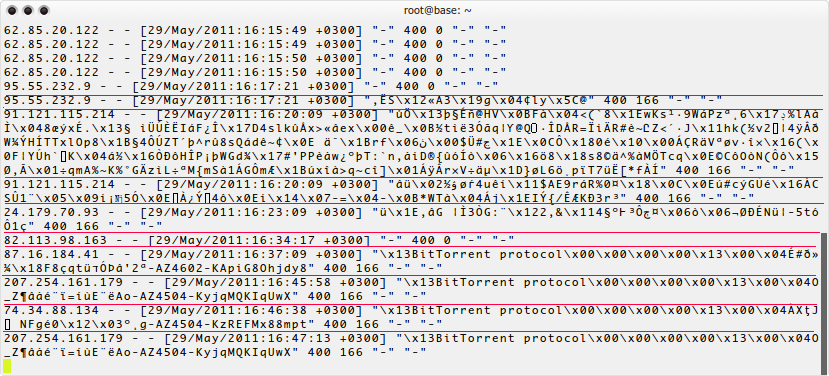
Since I specified my webserver’s port 80 as a target, I can see all the Bittorrent handshakes in my Nginx access log.
And even after about 6 months I still get them a lot. 🙂
This clearly shows that public Bittorrent network is full of crap. Probably in most countries you won’t be too worried about this but you never know what and when they intend to do with this data.
So what can you do?
If you have blocked incoming connections, no need to worry (but this also makes it harder to download and share stuff). In other cases using random ports each time you start your Bittorrent client could help a bit.
Also using not so popular and private Bittorrent trackers should be safer. Another nice thing about them is that they usually have some high speed servers dedicated for seeding torrents resulting in faster download speeds for you.
un ja piespiedu protokola šifrēšanu ar izslēgtiem legacy conections ?
tad ar var jabūt briesmās ?
Protokola šifrēšana nepalīdz, jo tie boti sūta handshake arī šifrētā versijā.